Contracts Law: Nature, Classification, Agreement, and Consideration
When it comes to contract law, there’s a lot of information that covers everything from the basics to specific elements of a contract.
Contract Law Basics
Contract law is sourced from Common law, except in certain cases when contracts are modified by statutory law such as UCC (Uniform Commercial Code). At its core, a contract is an agreement—fundamental to business functions by establishing a binding relationship between parties. Contracts are used for outlining what that agreement looks like by creating rights and duties between parties, in the form of a promisor (party who extends an offer or promise), and the promisee (party who accepts it.)
An Agreement is formed between two or more parties, and once made, can be legally enforced in a court of law. If one or more parties fails to perform on the terms negotiated in the agreement, damages are owed to the other party. An agreement is only part of a contract though—additional elements include the contract’s legality, capacity, and consideration.
A Consideration is defined as “value given in exchange for a promise” and must be something of sufficient value exchanged for that promise. It is important for there to be an exchange of genuine value, or the exchange could be classified as a gift.
Capacity within contract law is whether an individual is considered legally able to make and keep contractual agreements. Minors and the mentally ill are examples of situations where people can be considered lacking the legal capacity to make “amendments to their rights, duties, and obligations” (for example, getting married).
Contract Legality means that the original contract entered into must be legal to be enforceable. Ensuring all elements of a contract are valid and legal avoids confusion or mistakes down the road. The contract must adhere to statutes and laws or it will never have been considered formed in the first place.
Contract Forming
There are many different types of contracts and a variety of ways to go about forming them. This is an overview of some of the more common kinds of contracts.
Bilateral and Unilateral Contracts
In a bilateral contract, a promisor and a promisee both mutually exchange promises to each other. Examples of bilateral contracts are common in everyday life. Bilateral contracts can be seen in retail purchases, doctor visits, or even checking out a book at the library. In all of these situations, one party promises a certain action to another party, essentially forming an unwritten agreement.
Unilateral contracts are a contract where the initial obligation only extends one way, with one party promising another something without any initial reciprocation. A common example of a unilateral contract is the “missing pet” case. If someone lost their dog and placed an ad in the newspaper, online, or on flyers offering a $1,000 reward, they offer a unilateral contract. This is a promise to pay if anyone fulfills the obligation initially requested of returning the dog. Only one person takes action as no one is specifically assigned to find the dog, but once someone does find it, the offer then becomes irrevocable and the promisor cannot withdraw the contract.
Formal and Informal Contracts
A formal contract is written agreements between two parties that is legally binding and can be enforced by the law. Formal contracts contain an offer, the acceptance of that offer, and the conditions in regards to the materials associated with the offer.
Informal contracts are the opposite—anything that is not a formal contract. Informal contracts do not require any sort of legal intervention and are often referred to as social contracts. Verbal agreements are a form of informal contracts, but should only be made if both parties are trusted to keep their side of the agreement.
Accepting an Offer
Accepting an offer is the agreement to the terms of the offer made. This is where the mirror image rule comes into play. The mirror image rule means that unconditional acceptance of the offer is the only way to create a binding contract. Additional terms could be considered a counteroffer.
E-Contracts
As the cloud becomes a central, secure location for business to be done, contracting online, in turn, becomes more viable and secure. Signing and sending contracts digitally has become second nature for many companies, from small businesses to the Fortune 500. Most e-commerce companies use a type of contract to tender their services through the online agreement to terms and conditions as a buyer checks out. A “shrink wrap agreement” is another type of boilerplate contract that goes along with a product. Using the product is usually considered acceptance of the terms and conditions, or in some cases, checking a box to confirm the agreement has been read.
Electronic Signatures (E-Signatures)
E-signatures were made legal on the federal level by the E-Sign (2000) Act, giving digital legal documents the validity they needed to be considered legally enforceable. The acceptance of e-signatures opened up a whole new world for how contracts could not only be signed, but stored, renewed, and managed. Tools such as asymmetric cryptosystems help prevent hackers and breaches of security to maximize trust and safety.
Uniform Electronic Transactions Act
The Uniform Electronic Transactions Act (UETA) was established to help remove barriers inhibiting electronic commerce and establish the validity of electronic signatures and digital contracts. The act defines an electronic signature as “an electronic sound, symbol, or process attached to or logically associated with a record and executed or adopted by a person with the intent to sign that record.” The UETA paved the way in many regards for the E-Sign Act to be formed.
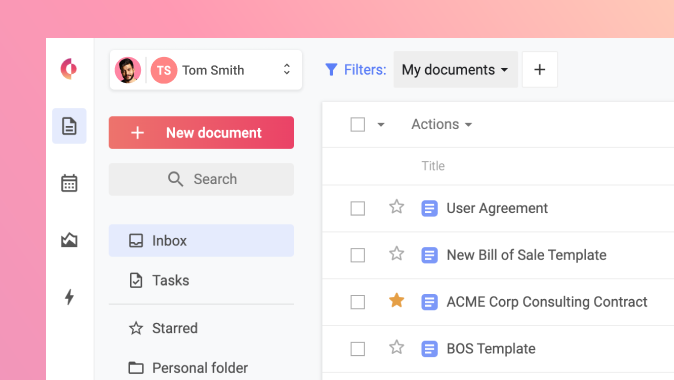
By now, the legality and security surrounding electronic contracts and signatures are well established. Using a cloud-based contract lifecycle management platform to manage, negotiate, and sign contracts is becoming the standard for organizations around the globe. To find out how your business can more effectively manage contracts digitally, click on the button below to request a demo.
Request demo